By now, you’re probably familiar with DORA (Digital Operational Resilience Act) and what it means for financial services. It’s not just another regulation. It’s about proving that resilience efforts actually work.

In our first blog, we covered the basics of DORA and Threat-Led Penetration Testing (TLPT), who it applies to, and why it matters. Now, we’re focusing on what compliance involves and how to approach it in a way that’s both effective and practical.
If DORA is on your radar, this guide will help you break down the key steps, understand the impact, and make sure your organisation is on the right track.
DORA Compliance: What Does It Actually Require?
Unlike traditional compliance frameworks that focus on security controls and best practices, DORA demands operational resilience. It ensures that financial institutions can continue running even when a cyberattack, IT failure, or operational disruption occurs.
We mentioned in part 1, that for high-risk institutions, this means meeting strict testing requirements, including Threat-Led Penetration Testing (TLPT). We know that TLPT isn’t just another security test—it’s a regulatory mandate, designed to mimic real-world attacks to uncover weaknesses before cybercriminals do.
Under DORA, compliance isn’t optional. From banks and insurance firms to ICT service providers and crypto platforms, organisations must be able to demonstrate their resilience. Those that fail to comply risk regulatory scrutiny, financial penalties, and reputational damage.
The Role of the TIBER-EU Certification Framework in TLPT
To fully meet DORA’s TLPT requirements, financial institutions need a structured and intelligence-driven approach to security testing. TIBER-EU (Threat Intelligence-Based Ethical Red Teaming) provides the framework to ensure TLPT exercises are conducted in a standardised, effective, and realistic way.
Why Was TIBER-EU DORA Created?
Before TIBER-EU, financial institutions across different EU countries used varying security testing frameworks. This led to inconsistencies, duplication of efforts, and potential gaps in Cyber Security testing. TIBER-EU was introduced to unify the approach across the financial sector, ensuring a higher standard of resilience testing.
The framework provides:
- A unified testing process for financial organisations across the EU.
- A structured, intelligence-led methodology for conducting TLPT.
- A focus on real-world attack simulations, using up-to-date cyber threat intelligence to identify vulnerabilities in an organisation’s people, processes, and technology.
How Does TIBER-EU Fit into DORA?
Under DORA (Regulation EU 2022/2554), financial institutions must conduct Threat-Led Penetration Tests (TLPT) at least once every three years. These tests must:
- Simulate real cyberattacks based on actual threat intelligence.
- Test critical financial infrastructure to assess resilience.
- Include third-party service providers (such as cloud and IT vendors) to evaluate supply chain security.
- Be conducted ethically following strict security protocols.
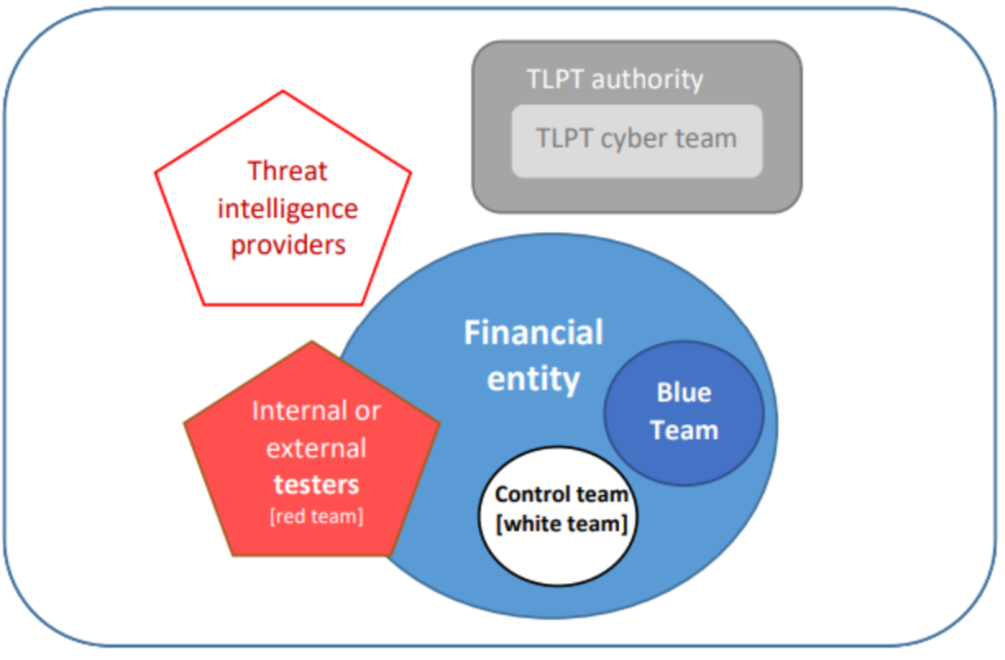
The Five Key Participants in a TLPT RTS (Based on TIBER-EU)
A Threat-Led Penetration Test involves multiple stakeholders, each playing a key role in the test process. The Final Report on the DORA RTS TLPT outlines the five key participant groups involved:
- 1. Financial Entity (the organisation being tested) – The institution undergoing TLPT, ensuring compliance and resilience.
- 2. Control Team (White Team) – The internal security team managing the TLPT exercise without revealing details to operational staff.
- 3. Blue Team – The organisation’s Security Operations Centre (SOC) or IT defence team, responsible for detecting and responding to simulated attacks.
- 4. Internal or External Testers (Red Team) – Ethical hackers conducting real-world attack simulations to assess defences.
- 5. Threat Intelligence Providers – External teams gathering intelligence on sector-specific cyber threats, ensuring the test mimics realistic attack scenarios.
This structured approach ensures that TLPT is more than just a standard pen test—it is a controlled, intelligence-led operation that reflects real-world cyber threats.
The threat led pen testing methodology: ESMA
TIBER-EU Testing Methodology: How TLPT Works in Practice
The TIBER-EU framework structures TLPT into three distinct phases:
The threat led pen testing process: ESMA
- 1. Threat Intelligence Phase
- The Threat Intelligence Provider collects intelligence on real cyber threats specific to the financial sector.
- Custom attack scenarios are created to reflect the most relevant risks.
- 2️. Red Teaming Phase
- Ethical hackers (the Red Team) simulate real-world attacks to test the institution’s defences.
- The Blue Team (defenders) are unaware of the test, ensuring a realistic evaluation of their detection and response capabilities.
- Simulated attacks include phishing, network exploitation, and supply chain intrusions.
- 3. Closure Phase
- A detailed report is compiled, outlining how well the organisation detected, responded to, and recovered from the attacks.
- The Control Team reviews the findings and prepares a remediation plan.
- The financial entity submits the results to regulators, ensuring compliance.
This structured approach ensures financial organisations get a realistic assessment of their security resilience while also meeting DORA’s strict compliance requirements.
TLPT vs Traditional Pen Testing: What’s the Difference?
Penetration testing has been a core security practice for years, but Threat-Led Penetration Testing (TLPT) takes things to a whole new level. While both approaches aim to identify weaknesses, their methods and objectives are vastly different.
How Traditional Penetration Testing Works
- Checklist-driven approach – Ethical hackers assess systems, networks, and applications against predefined test cases.
- Focuses on technical vulnerabilities – The goal is to find security flaws before attackers do.
- Limited scope – Typically tests a specific system or network in isolation.
- Controlled environment – Often conducted in test settings to avoid business disruption.
- Shorter engagement – A traditional pen test usually lasts a few weeks.
- Best practice, but not mandatory – While valuable, traditional pen testing isn’t a regulatory requirement under DORA.
How TLPT is Different
- Real-world attack simulation – Instead of just identifying vulnerabilities, TLPT mirrors actual cyber threats using up-to-date intelligence.
- Tests overall resilience – Focuses on how well an organisation can detect, respond to, and recover from an attack.
- Wider scope – Examines critical business functions and financial infrastructure, rather than just individual systems.
- Live production testing –TLPT is conducted in a real-world environment, making it more realistic but also more challenging.
- Regulatory requirement under DORA – High-risk financial institutions must conduct TLPT every three years.
- Longer, more complex process – TLPT involves months of intelligence gathering, attack simulations, and regulatory oversight.
The stakes are high. If an attacker gains access to critical financial infrastructure, it’s not just an IT issue—it’s a risk to financial stability. That’s why DORA mandates TLPT, ensuring financial institutions aren’t just compliant on paper, but truly resilient against cyber threats.
Inside a TLPT: A Real-World Business Case
A large European bank was preparing for its first Threat-Led Penetration Test (TLPT) under DORA. They had strong security controls, a dedicated Security Operations Centre (SOC), and regular penetration tests—but they had never faced an attack designed to mirror real-world cybercriminal tactics.
The test began with threat intelligence gathering, identifying risks specific to the bank. The Red Team (ethical hackers) crafted a scenario based on recent financial sector breaches—a phishing attack targeting executives and a supply chain compromise through an IT service provider.
Within days, an employee unknowingly entered credentials into a fake login portal, giving the attackers initial access. From there, the Red Team exploited a weak third-party connection to move deeper into the bank’s systems, gaining access to customer payment processing.
For hours, the SOC remained unaware of the breach. Automated alerts flagged suspicious activity, but slow detection and response times allowed the attackers to escalate their access. When the attack was finally contained, it was clear—a real-world breach could have resulted in major financial losses.
The TLPT report highlighted critical weaknesses:
- Supply chain vulnerabilities — third-party access wasn’t well-monitored.
- Slow response times — the SOC took too long to react to red flags.
The bank submitted a remediation plan to regulators, improving staff training, third-party risk assessments, and incident response procedures. TLPT proved to be more than just compliance—it revealed real weaknesses before an actual attack could exploit them.
Are You Truly Resilient, or Just Compliant?
DORA isn’t just another regulation. It’s a chance for financial institutions to show they can handle real-world cyber threats. Threat-Led Penetration Testing (TLPT) isn’t just about ticking a compliance box. It’s about finding and fixing weaknesses before attackers do.
In this blog, we’ve looked at how DORA brings TLPT into the picture, the role of the TIBER-EU framework, how TLPT differs from standard penetration testing, and what happens in a real-world engagement. The key takeaway? Security isn’t just about having the right controls in place. It’s about making sure they work when tested against realistic threats.
If you’re working on DORA compliance, now’s a good time to take stock. Can your SOC spot and respond to a live attack? Are your third-party providers meeting resilience expectations? Do you have the right support to make TLPT work for you? Done right, TLPT isn’t just about meeting a requirement. It’s a powerful way to strengthen your organisation’s defences and build confidence in your security strategy.
Let’s talk about your Cyber Security strategy. Call us on 0121 663 0055 or email enquiries@equilibrium-security.co.uk to get started.
Ready to achieve your security goals? We’re at your service.
expertise to help you shape and deliver your security strategy.
About the author